analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
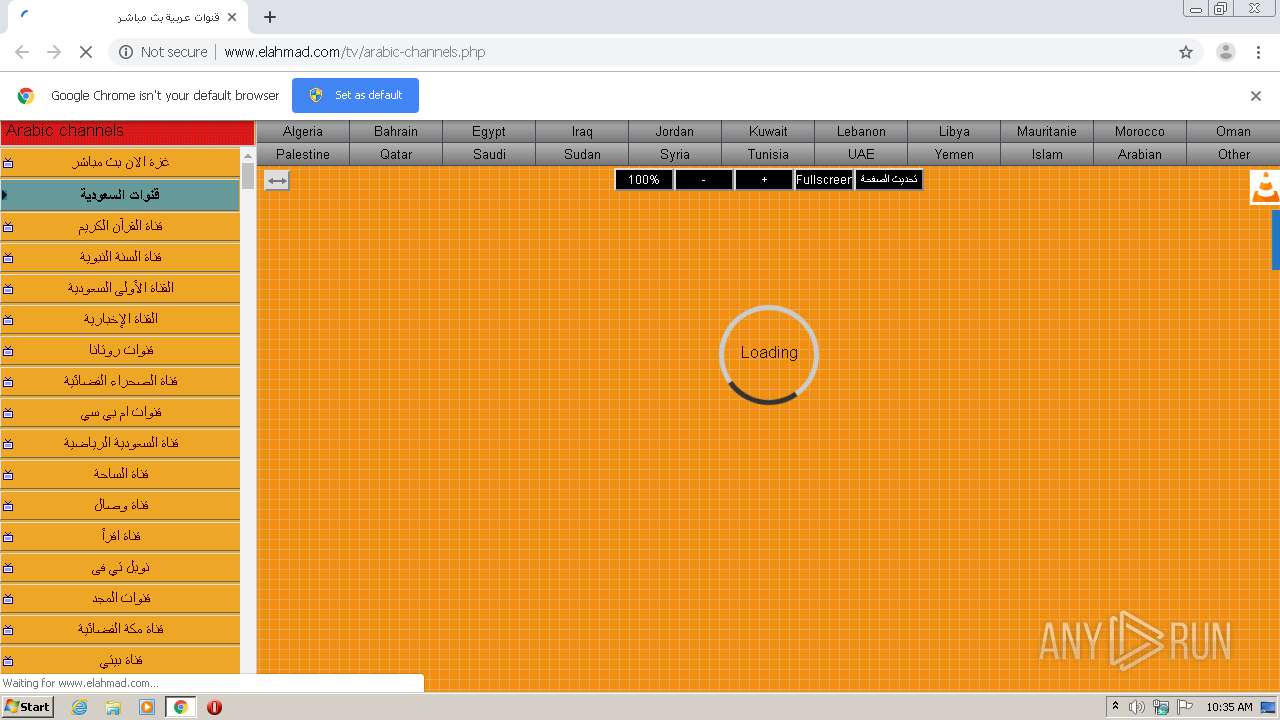
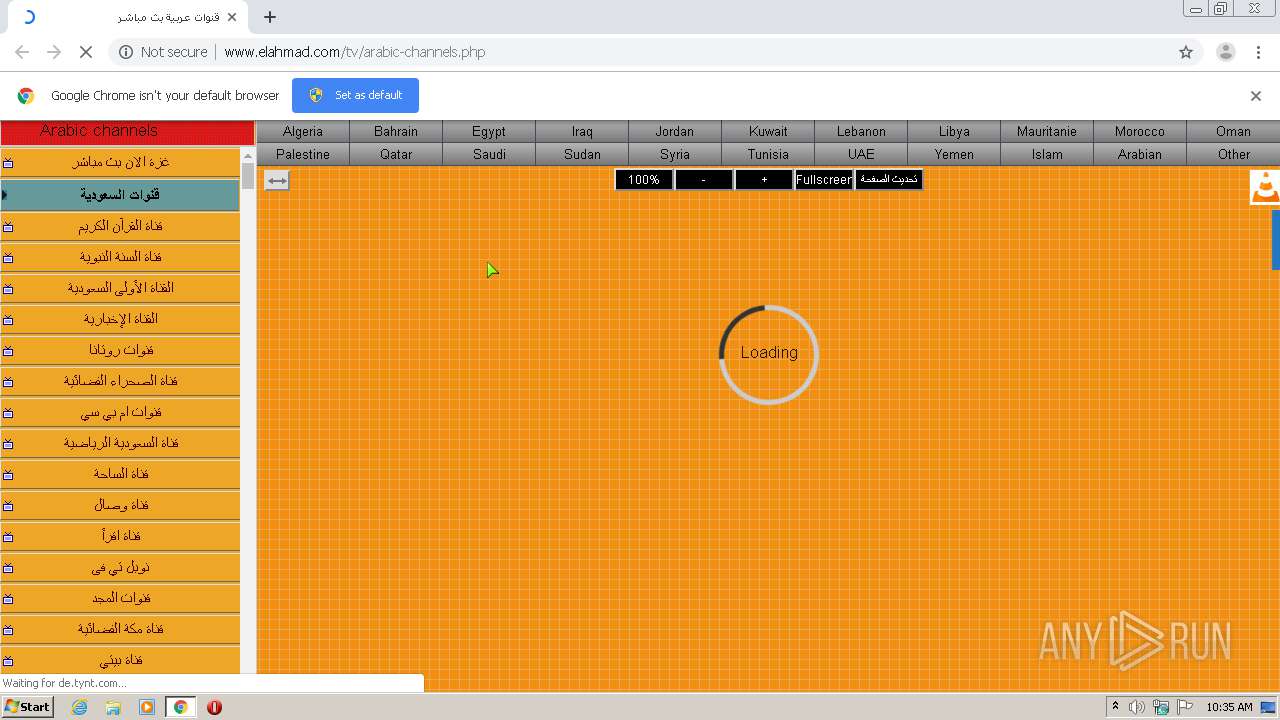
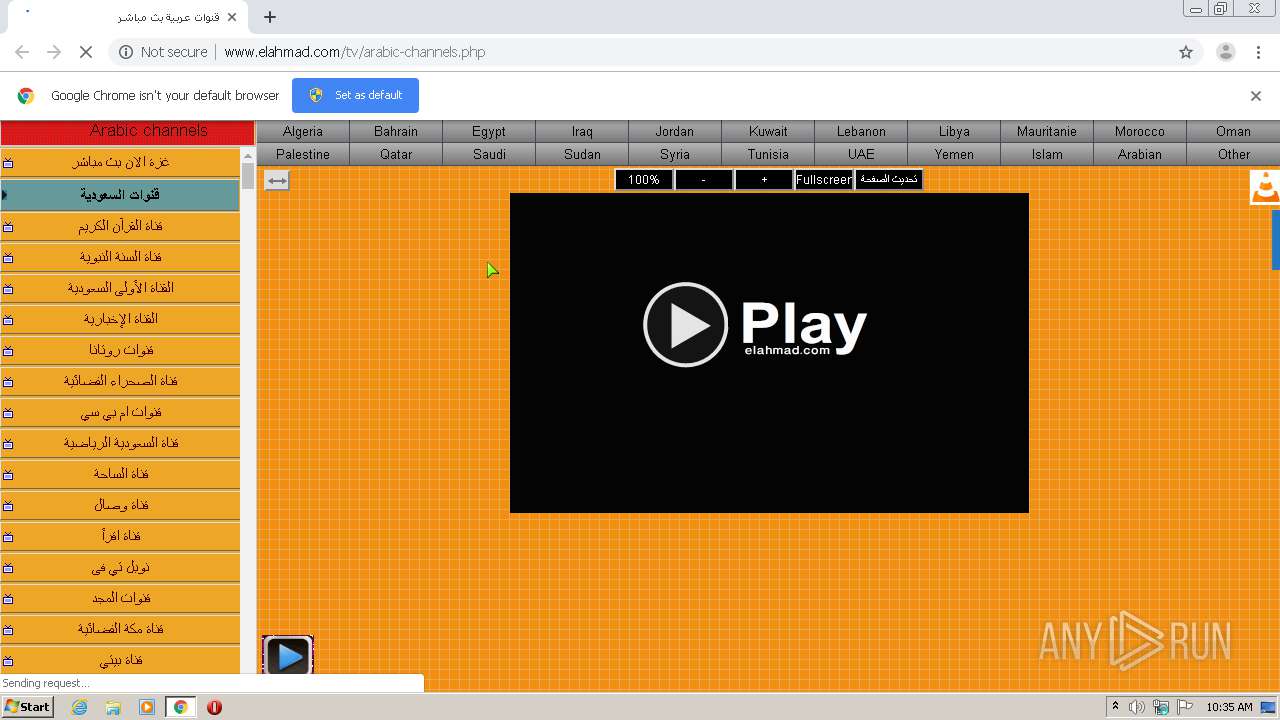
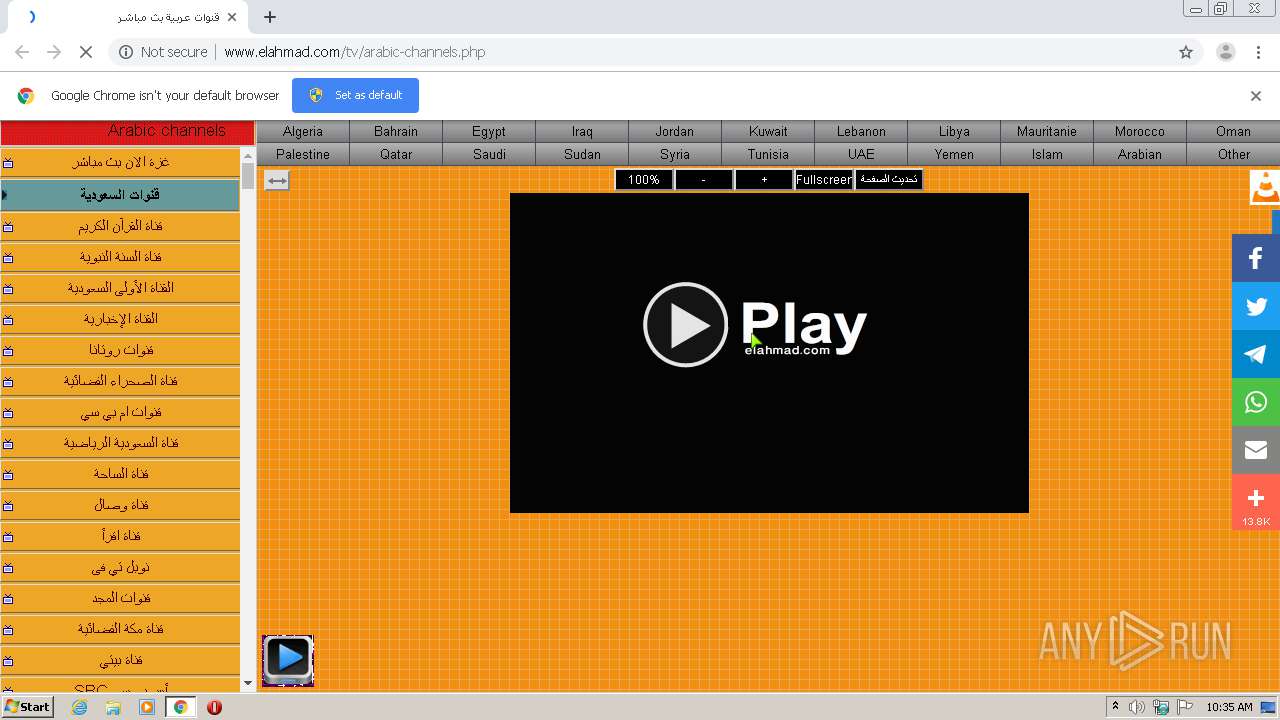
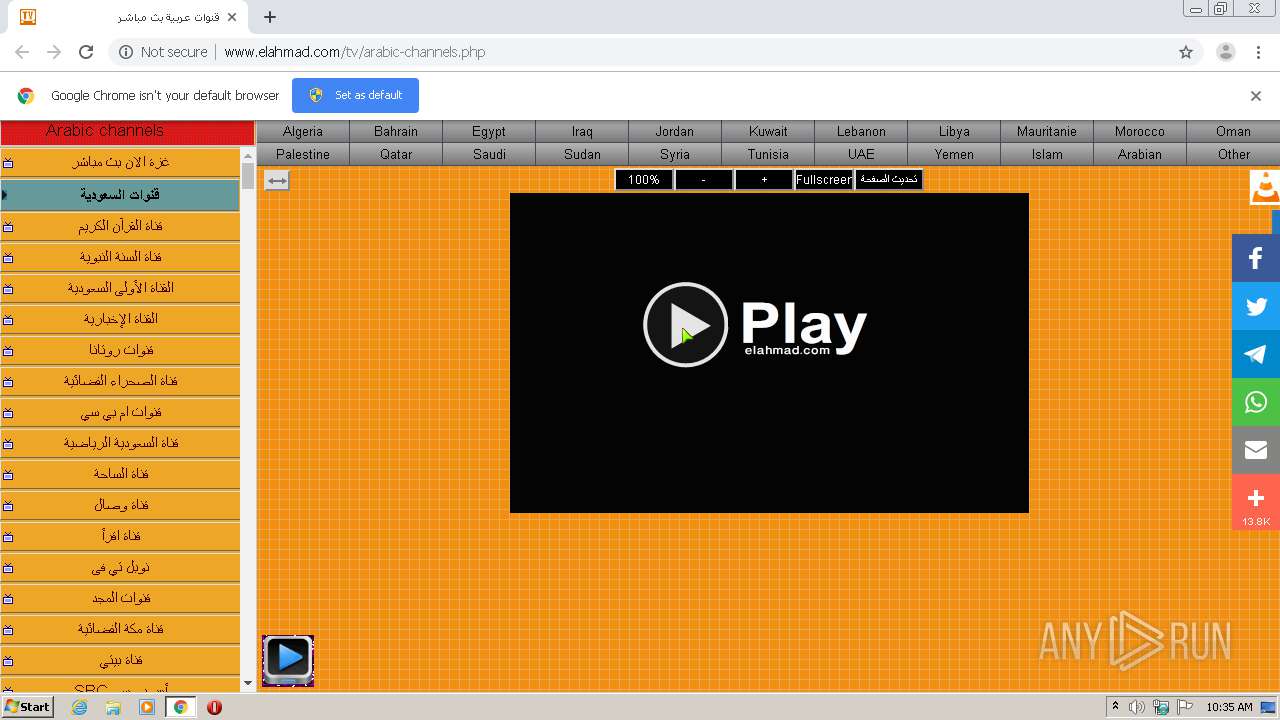
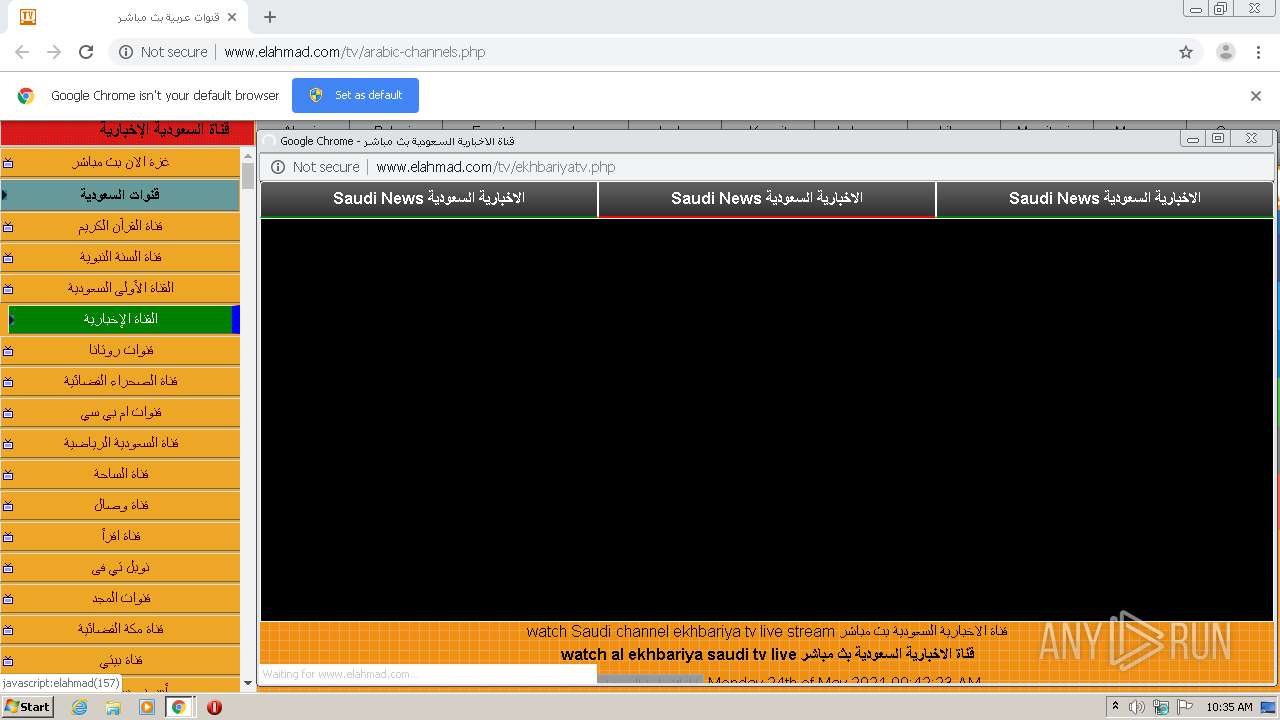
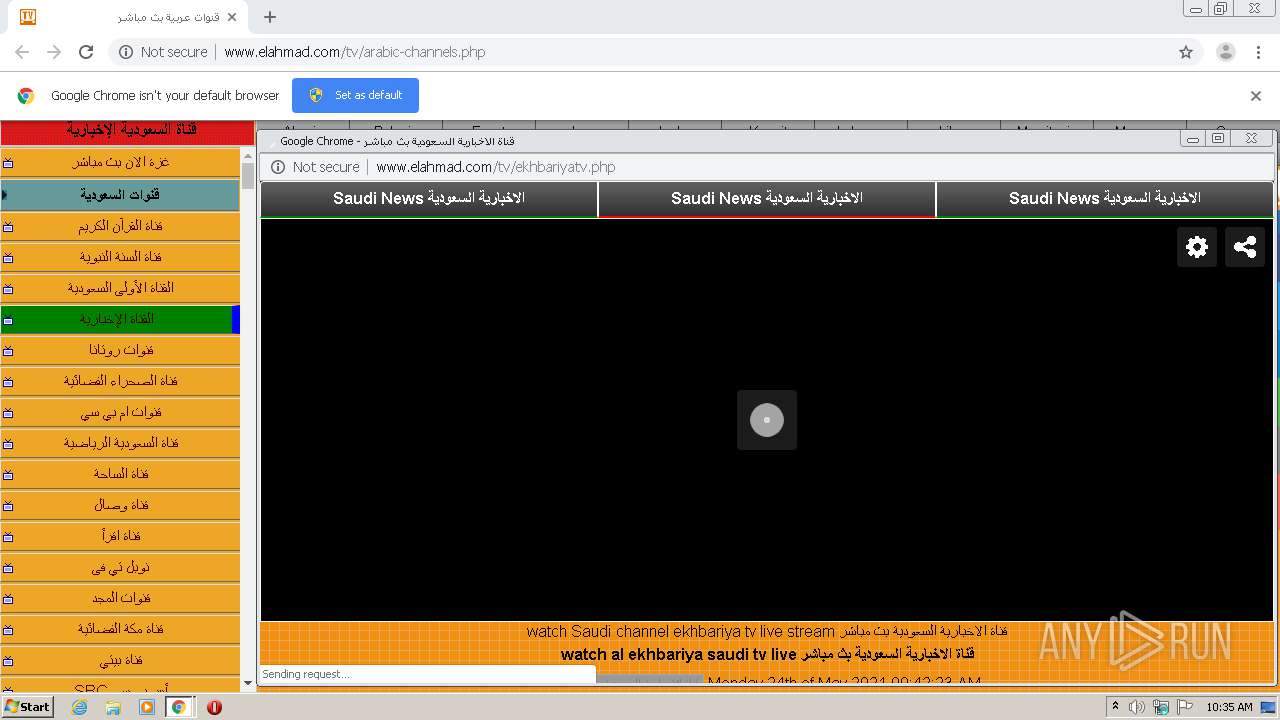
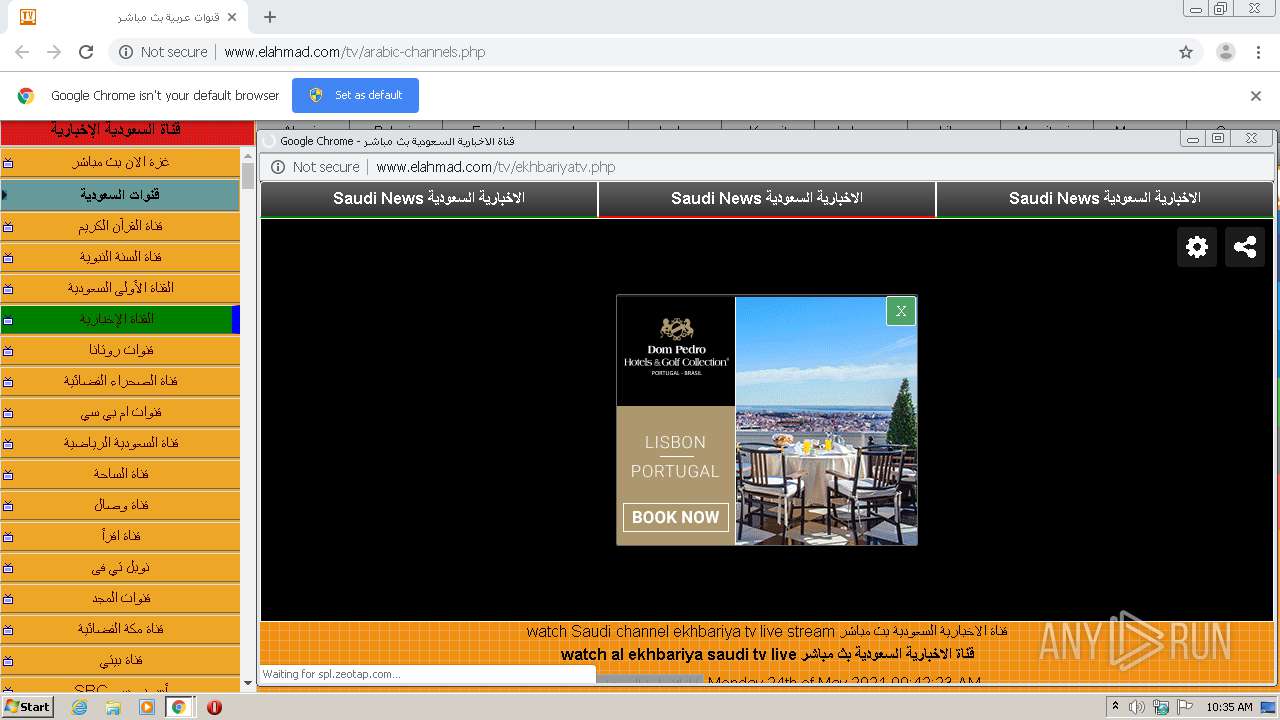
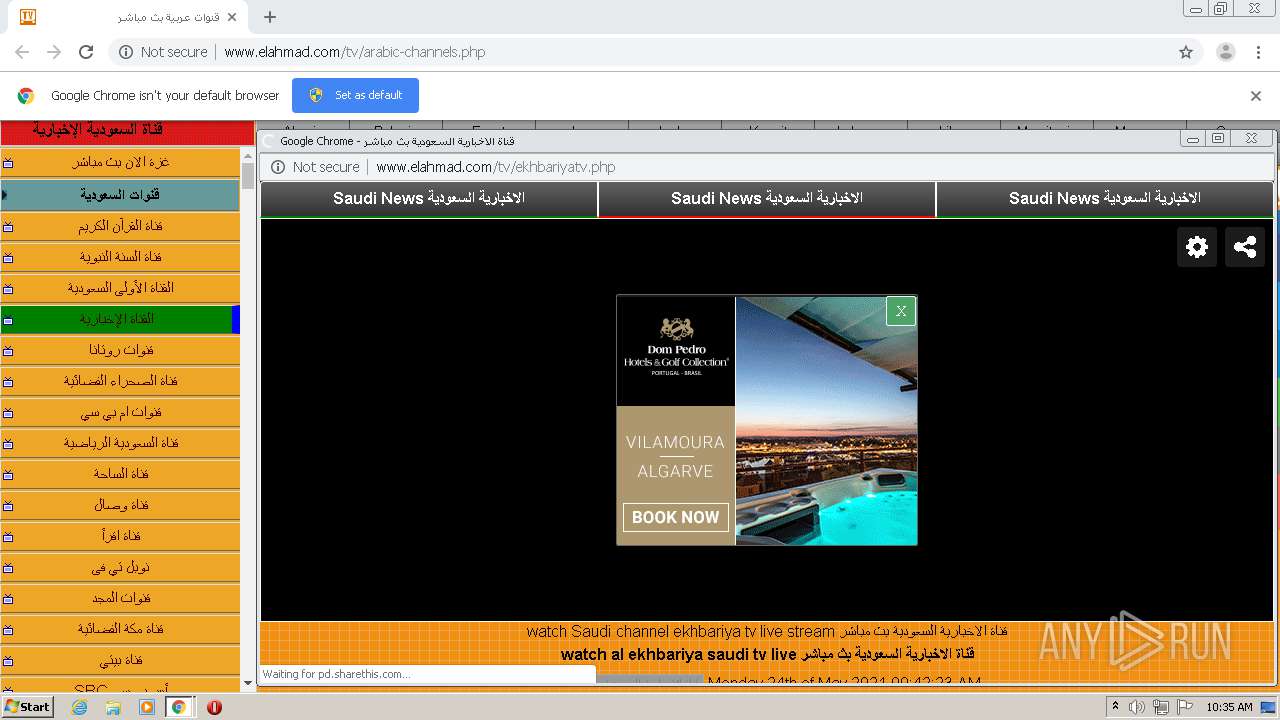
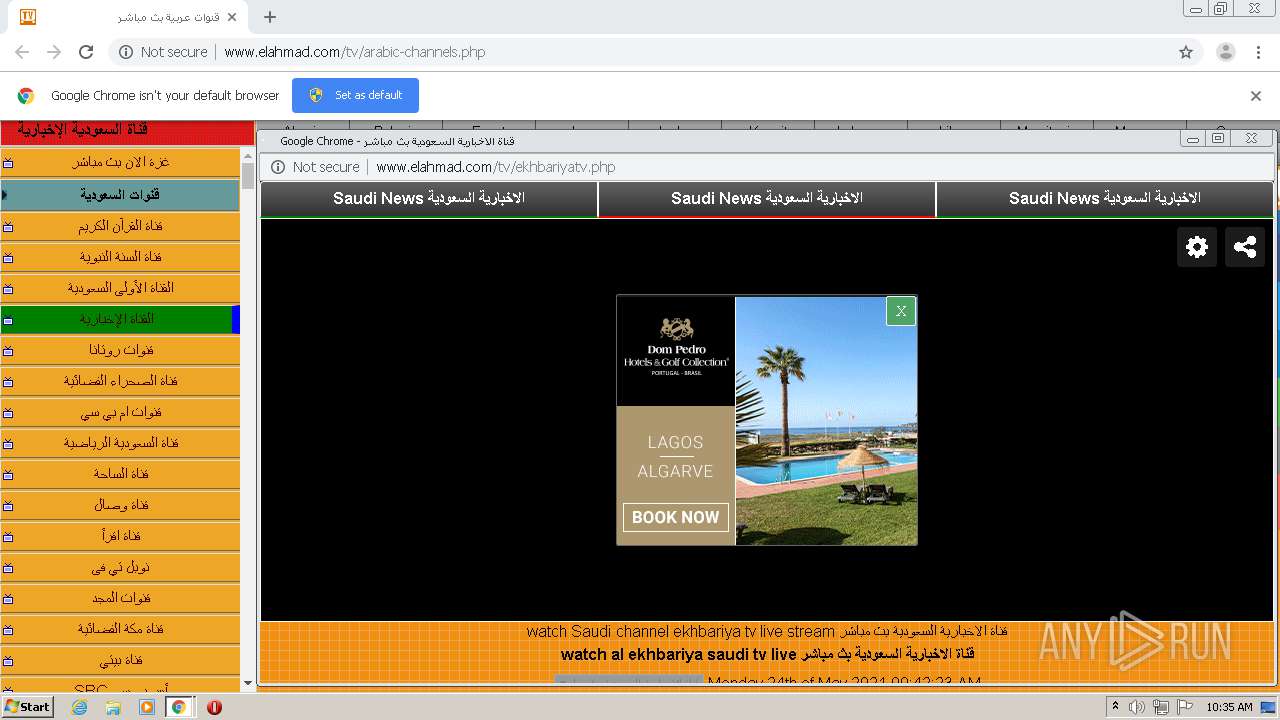
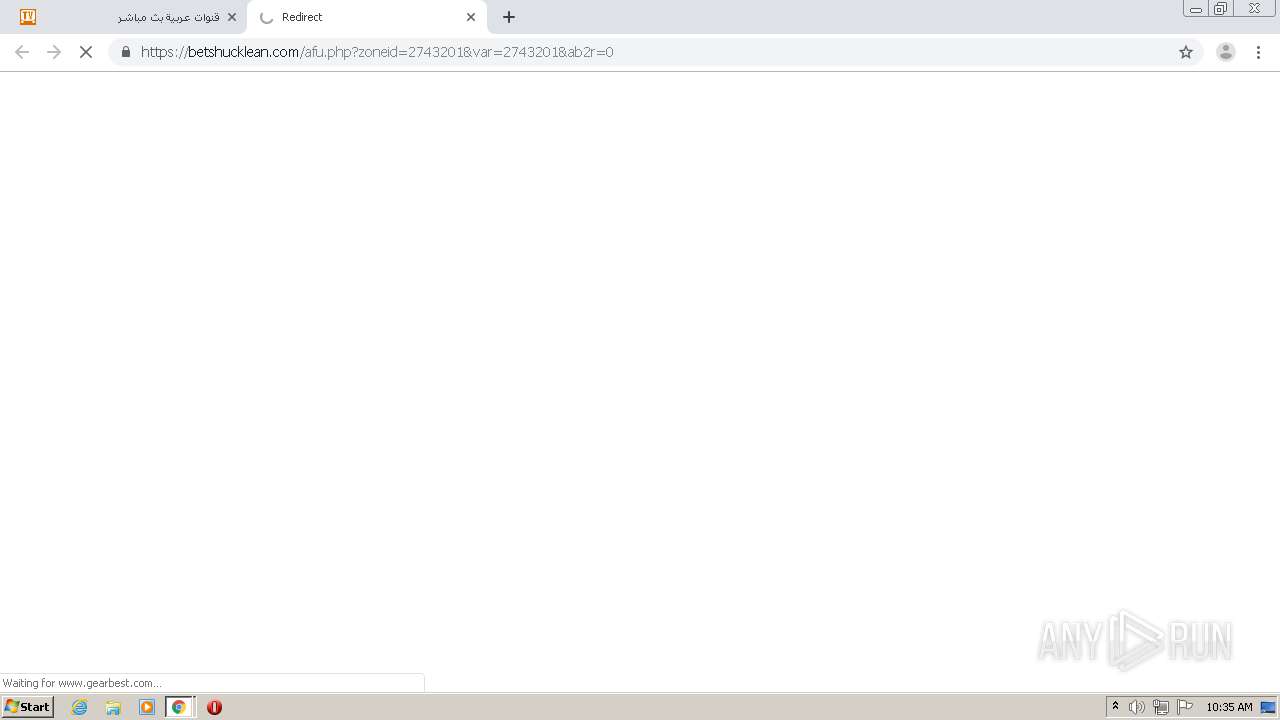
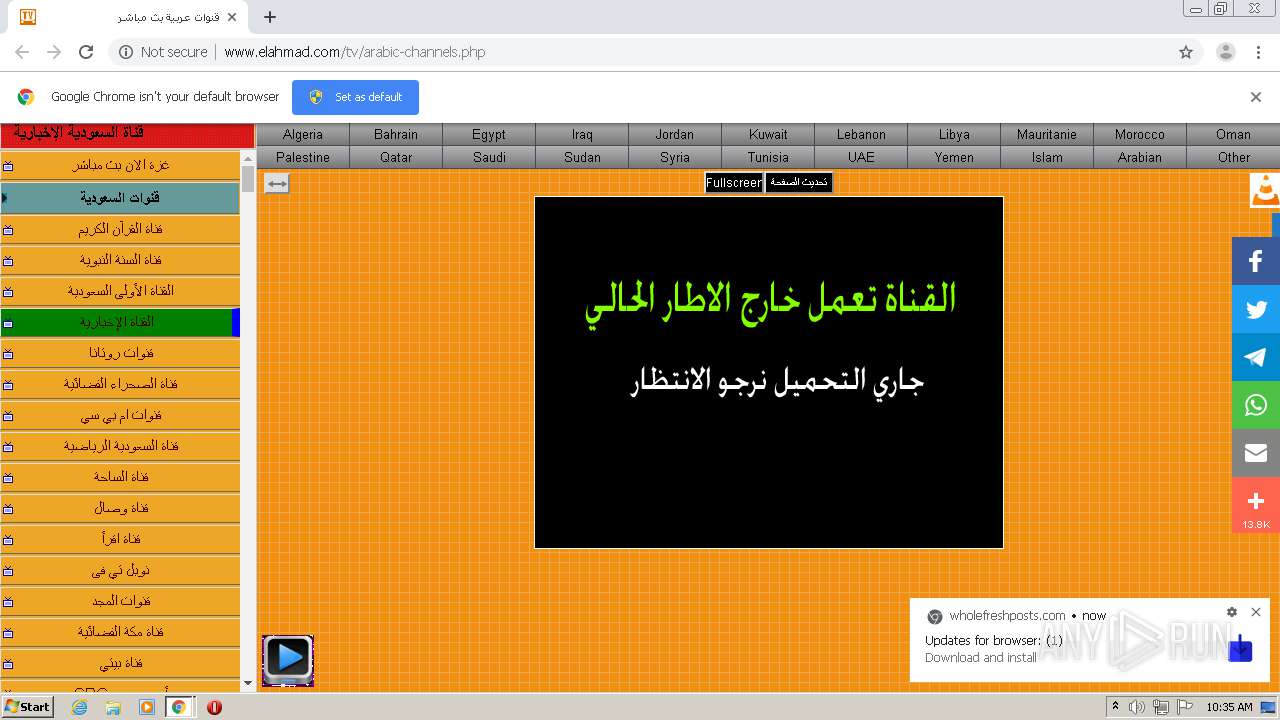
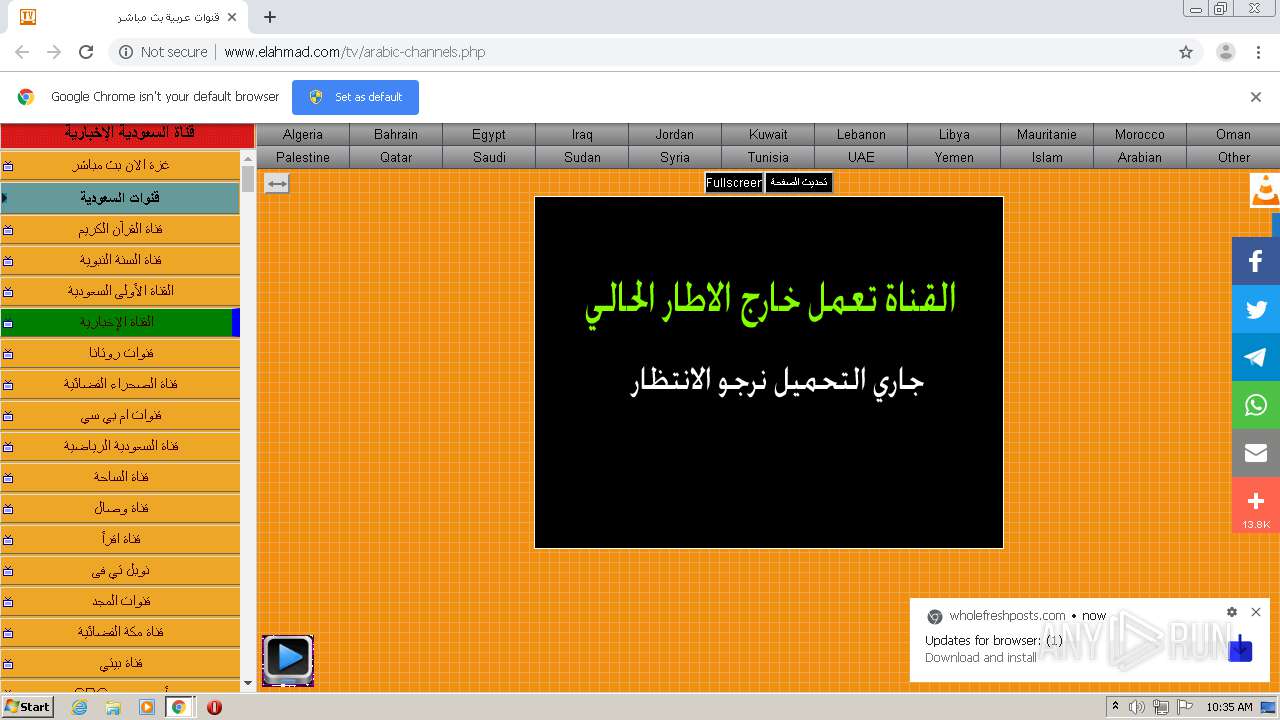
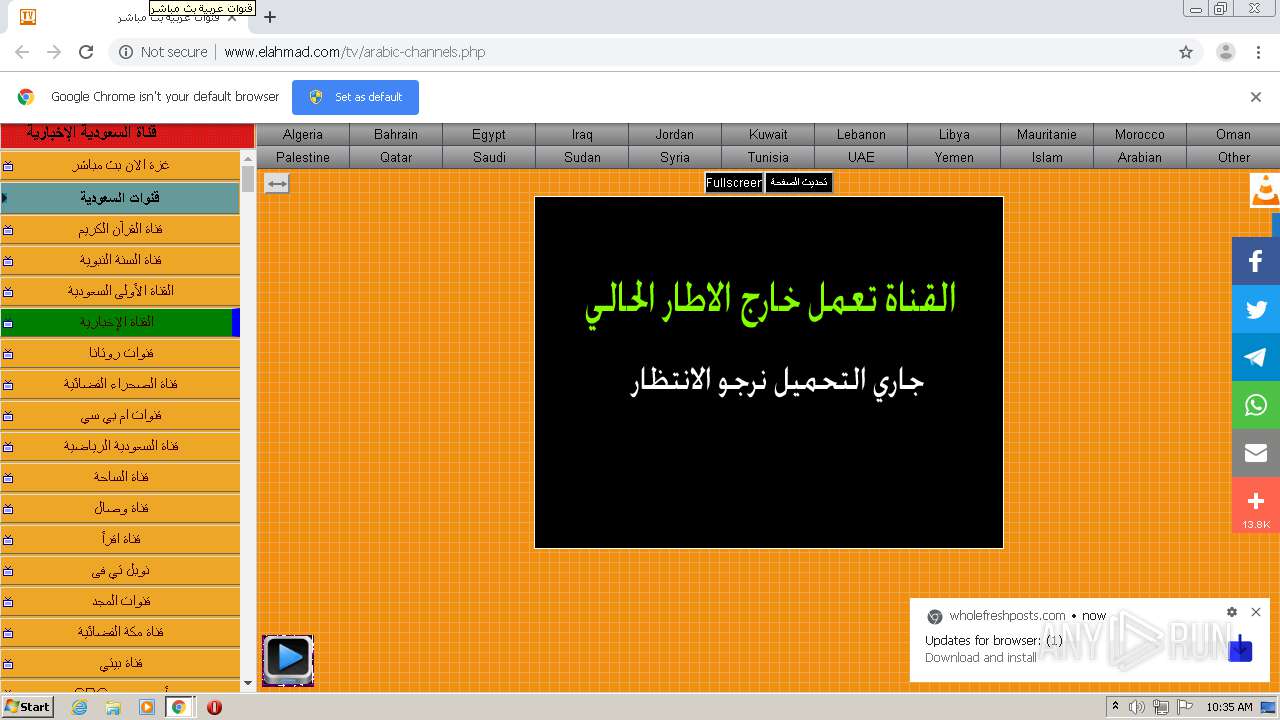
| URL: | http://www.elahmad.com/tv/arabic-channels.php |
| Full analysis: | https://app.any.run/tasks/ec82cc74-6a3a-4833-8c61-5214afc865bd |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2021, 09:34:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5AF352BA7C7DEBA9E55C918DB34B14D2 |
| SHA1: | 3B22B7D57606AB8530E3D55811125F45386552F5 |
| SHA256: | 80C67FC21B58AC63E5EE4C54954462AD3F3077AFD8C6EB32E167B03B1BFEC2B6 |
| SSDEEP: | 3:N1KJS4XXfXuonAYbV:Cc4XPbAa |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
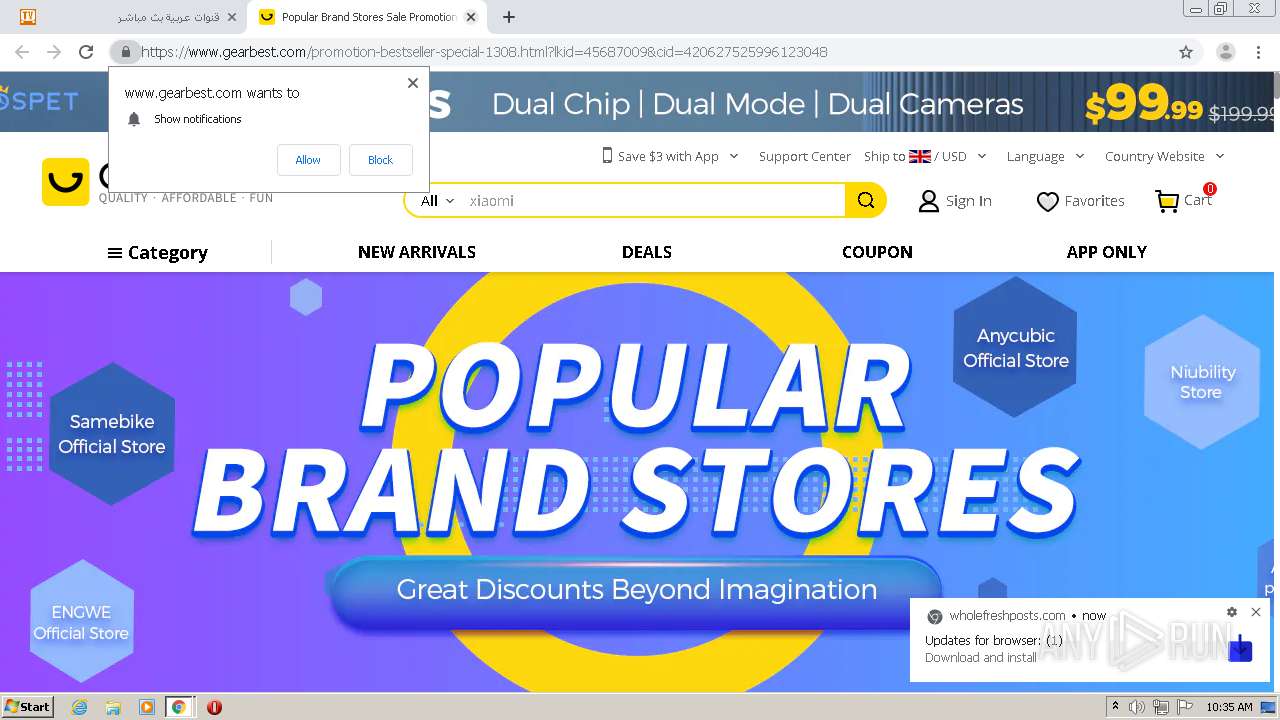
Reads the hosts file
- chrome.exe (PID: 2000)
- chrome.exe (PID: 2036)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2000)
Application launched itself
- chrome.exe (PID: 2000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
25
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://www.elahmad.com/tv/arabic-channels.php" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6bf0a9d0,0x6bf0a9e0,0x6bf0a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1980 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,17762075839436737447,2274928923495664545,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=583741282695963869 --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17762075839436737447,2274928923495664545,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17396346803495139257 --mojo-platform-channel-handle=1552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17762075839436737447,2274928923495664545,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5263640497511119584 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17762075839436737447,2274928923495664545,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13330487105476557118 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17762075839436737447,2274928923495664545,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1253529940718537174 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17762075839436737447,2274928923495664545,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=433338235526266310 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2944 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17762075839436737447,2274928923495664545,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8613071807795469257 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
644
Read events
572
Write events
69
Delete events
3
Modification events
| (PID) Process: | (2000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2000-13266322499321250 |
Value: 259 | |||
| (PID) Process: | (2000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2000) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
147
Text files
79
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60AB7344-7D0.pma | — | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\630e14c0-dc58-4ee6-bb09-89f9e22a84ce.tmp | — | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | text | |
MD5:74D4DB05A4D3E7263E8AE314DEDD8DF1 | SHA256:67BF9950E818713E054268D40BED61A22D324385CE98E89DDF406A405B870802 | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:F1220A80653B6B89B42DFD1B2E8155C3 | SHA256:36BBBC13CC1901CF269B4CE36E2EE08946806DFA58474AE88287CA8E9DA9725D | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFf0565.TMP | text | |
MD5:67F45CAA18C889645F50CD6216C81E65 | SHA256:33ED82CDDDFFD55A5059C147C6CD20F66C6712314F890A39576D3C10914D0029 | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:E815400F953EA8DB8A98D52737C9A50D | SHA256:E9F064927A191500B7365F51C9CD0763A6A8E68A8B866ACED39AA0E72C3EAD85 | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFf0537.TMP | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
66
TCP/UDP connections
167
DNS requests
111
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2036 | chrome.exe | GET | 200 | 37.59.71.101:80 | http://www.elahmad.com/images/hover.gif | FR | image | 62 b | suspicious |
2036 | chrome.exe | GET | 200 | 37.59.71.101:80 | http://www.elahmad.com/js.php | FR | text | 2.47 Kb | suspicious |
2036 | chrome.exe | GET | 200 | 37.59.71.101:80 | http://www.elahmad.com/js/extreme.js?v=100259723 | FR | text | 8.62 Kb | suspicious |
2036 | chrome.exe | GET | 200 | 37.59.71.101:80 | http://www.elahmad.com/tv/jsnews/functions.js?v=0.3 | FR | text | 33.5 Kb | suspicious |
2036 | chrome.exe | GET | 200 | 37.59.71.101:80 | http://www.elahmad.com/images/icon_wide.png | FR | image | 226 b | suspicious |
2036 | chrome.exe | GET | 200 | 37.59.71.101:80 | http://www.elahmad.com/tv/jsnews/tv.css?v=1 | FR | text | 7.44 Kb | suspicious |
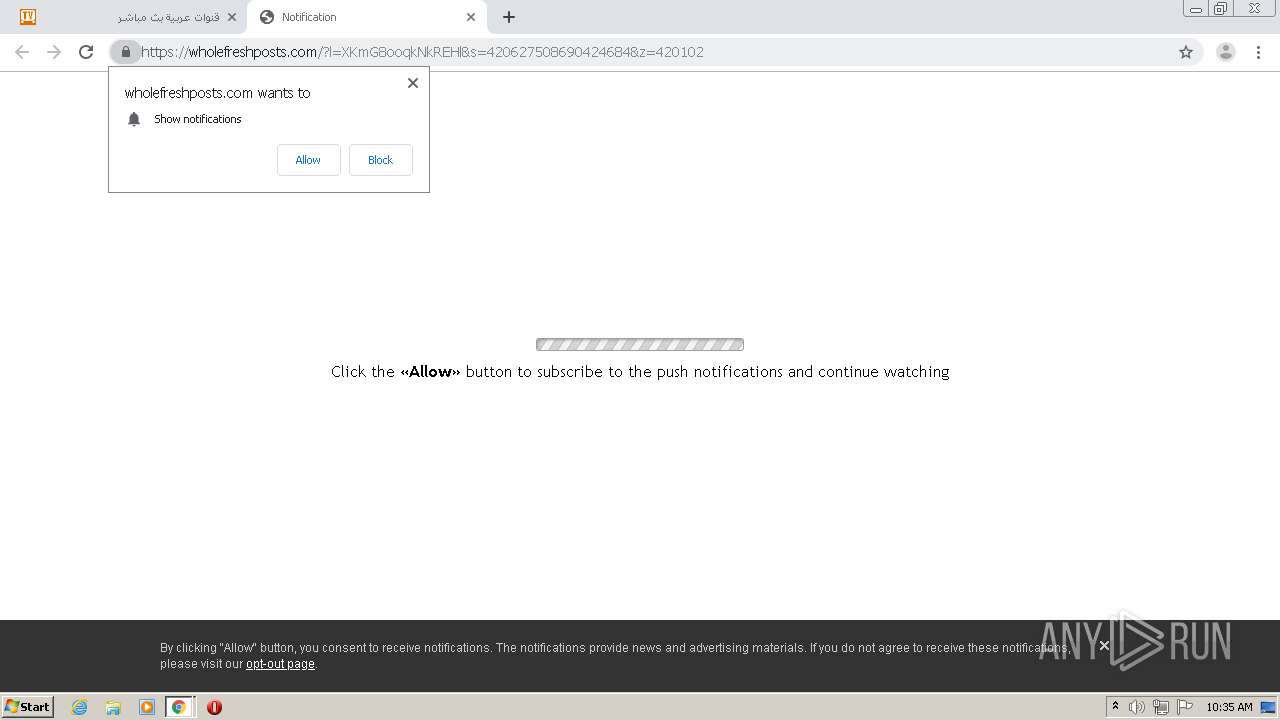
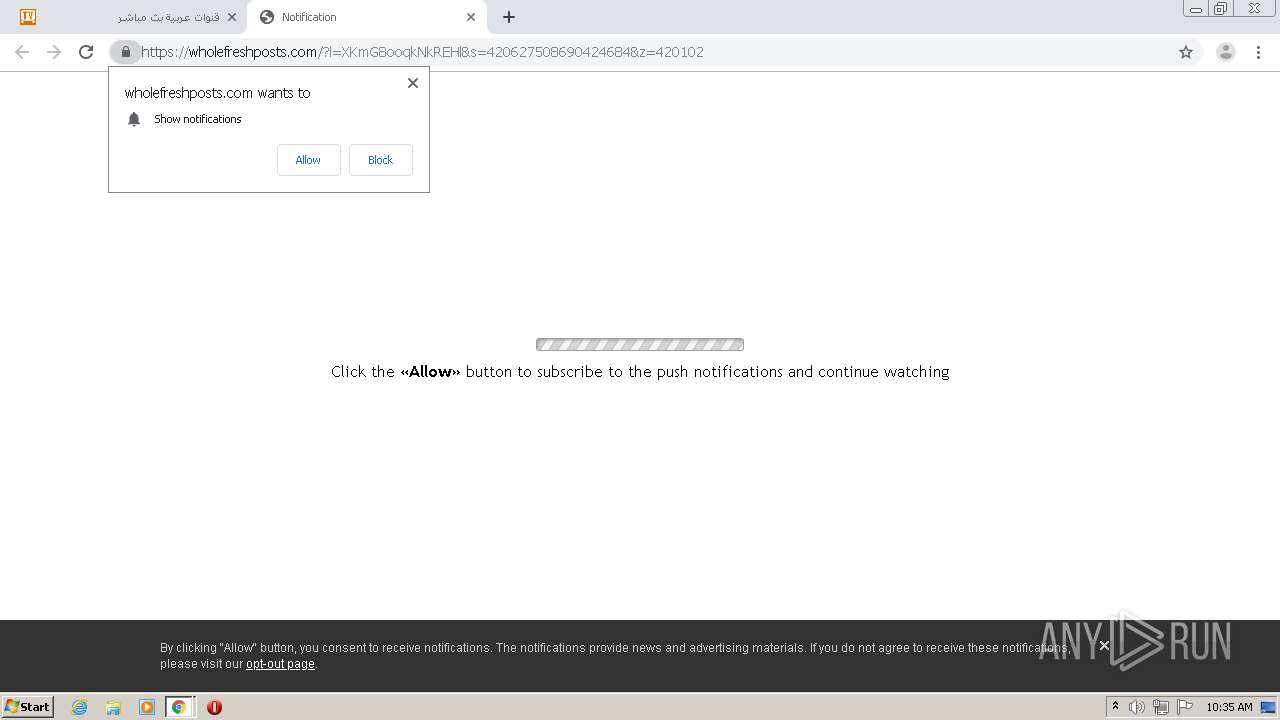
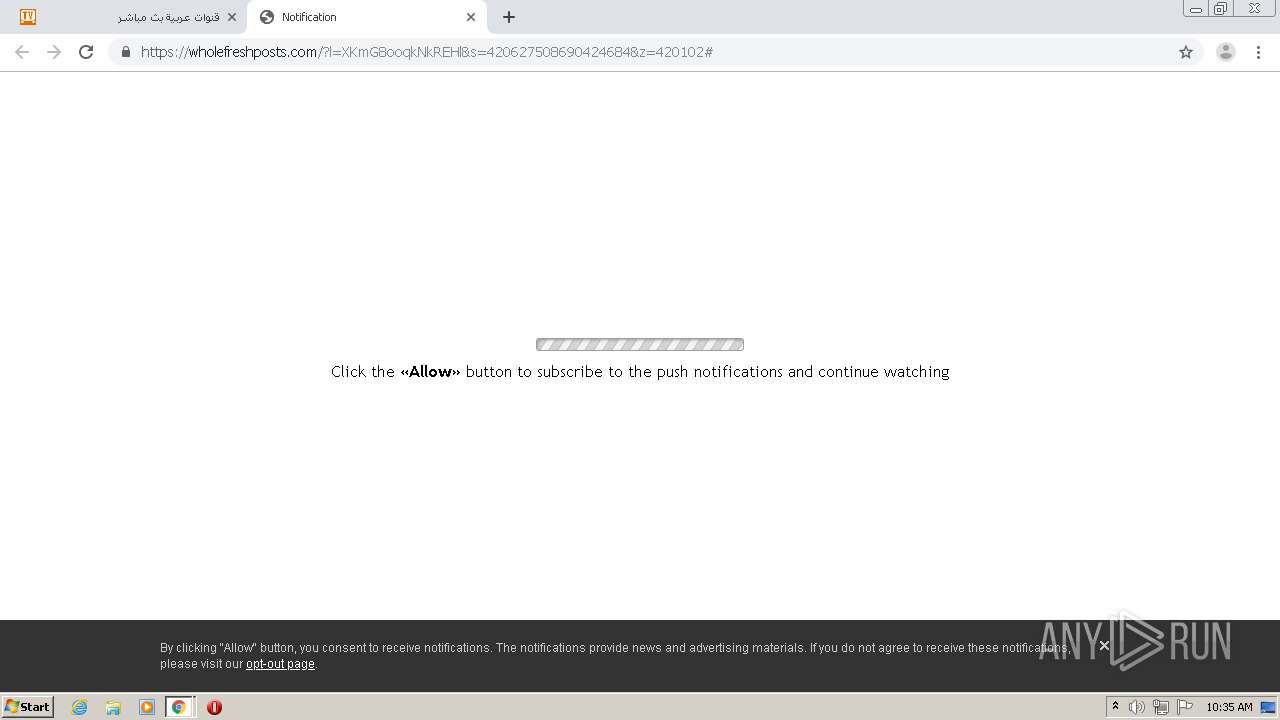
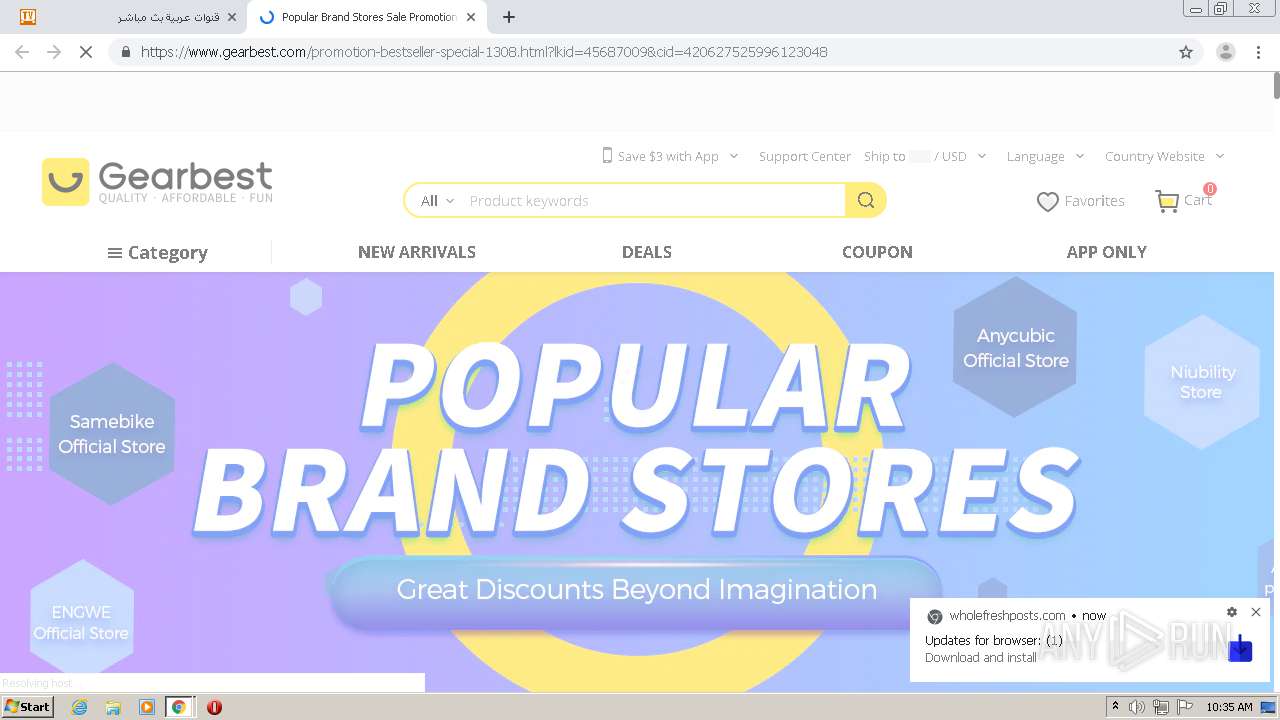
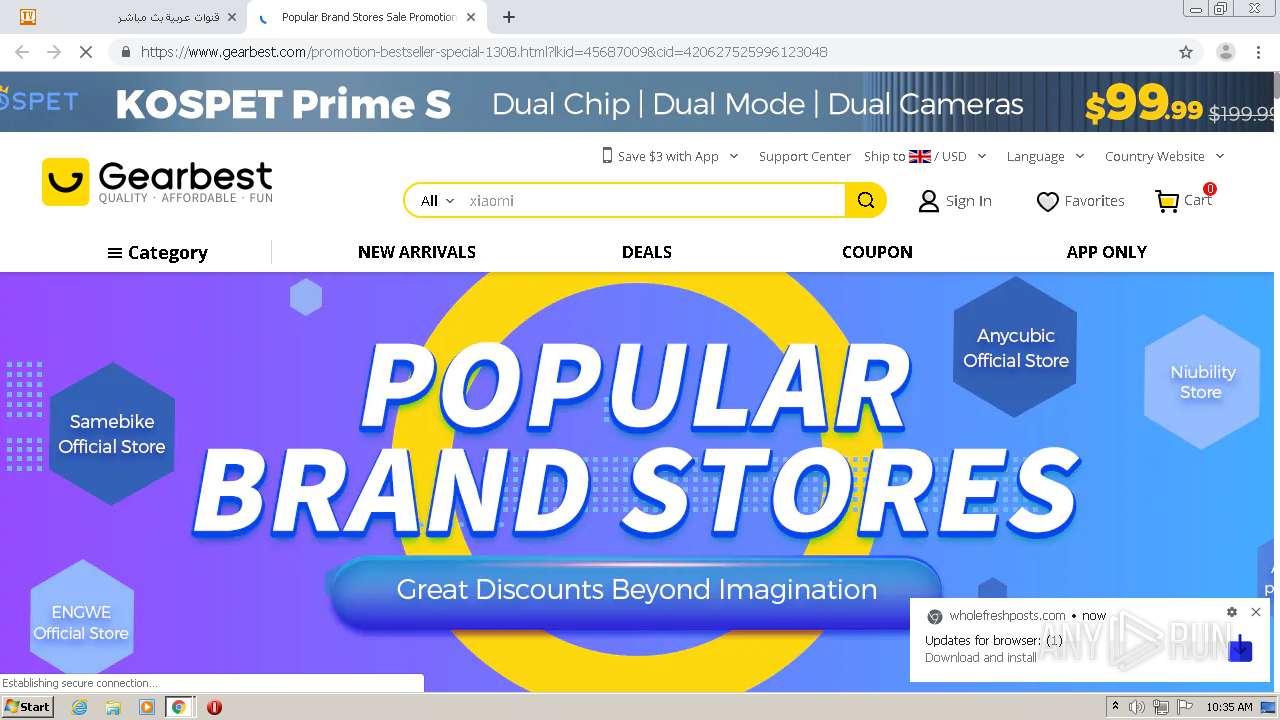
2036 | chrome.exe | GET | 200 | 104.21.40.11:80 | http://htintpa.tech/c/elahmad.com.js | US | text | 1.04 Kb | malicious |
2036 | chrome.exe | GET | 200 | 37.59.71.101:80 | http://www.elahmad.com/tv/arabic-channels.php | FR | html | 44.3 Kb | suspicious |
2036 | chrome.exe | GET | 200 | 37.59.71.101:80 | http://www.elahmad.com/tv/Pictures/tv.gif | FR | image | 73 b | suspicious |
2036 | chrome.exe | GET | 200 | 37.59.71.101:80 | http://www.elahmad.com/images/ad/tvlive1.png | FR | image | 2.13 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2036 | chrome.exe | 142.250.185.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2036 | chrome.exe | 151.101.1.44:80 | cdn.taboola.com | Fastly | US | suspicious |
2036 | chrome.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
— | — | 104.87.16.123:80 | s7.addthis.com | Akamai Technologies, Inc. | NL | unknown |
2036 | chrome.exe | 151.101.1.44:443 | cdn.taboola.com | Fastly | US | suspicious |
2036 | chrome.exe | 37.59.71.101:80 | www.elahmad.com | OVH SAS | FR | unknown |
2036 | chrome.exe | 172.67.191.144:80 | palibs.tech | — | US | unknown |
2036 | chrome.exe | 198.27.80.143:443 | — | OVH SAS | CA | suspicious |
2036 | chrome.exe | 104.87.16.123:443 | s7.addthis.com | Akamai Technologies, Inc. | NL | unknown |
2036 | chrome.exe | 104.21.40.11:80 | htintpa.tech | Cloudflare Inc | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.elahmad.com |
| suspicious |
accounts.google.com |
| shared |
cdnjs.cloudflare.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
s10.histats.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
htintpa.tech |
| malicious |
s4.histats.com |
| whitelisted |
palibs.tech |
| suspicious |
cdn.taboola.com |
| whitelisted |