analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
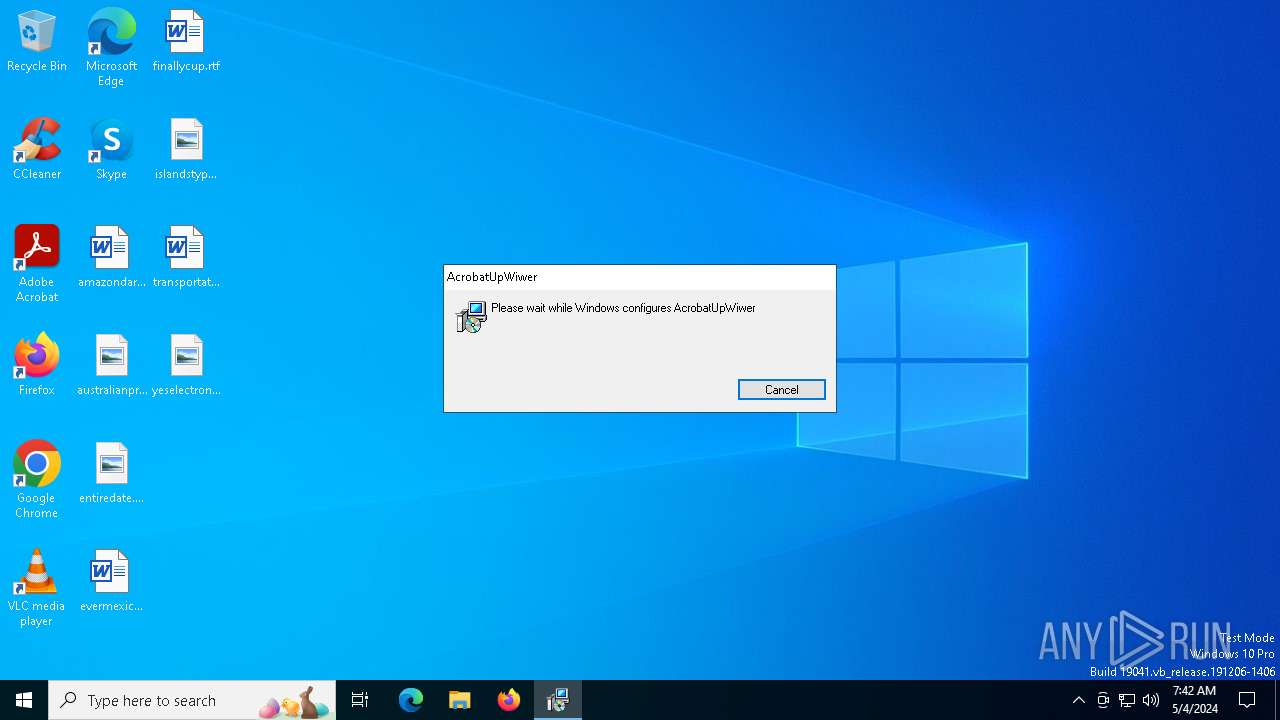
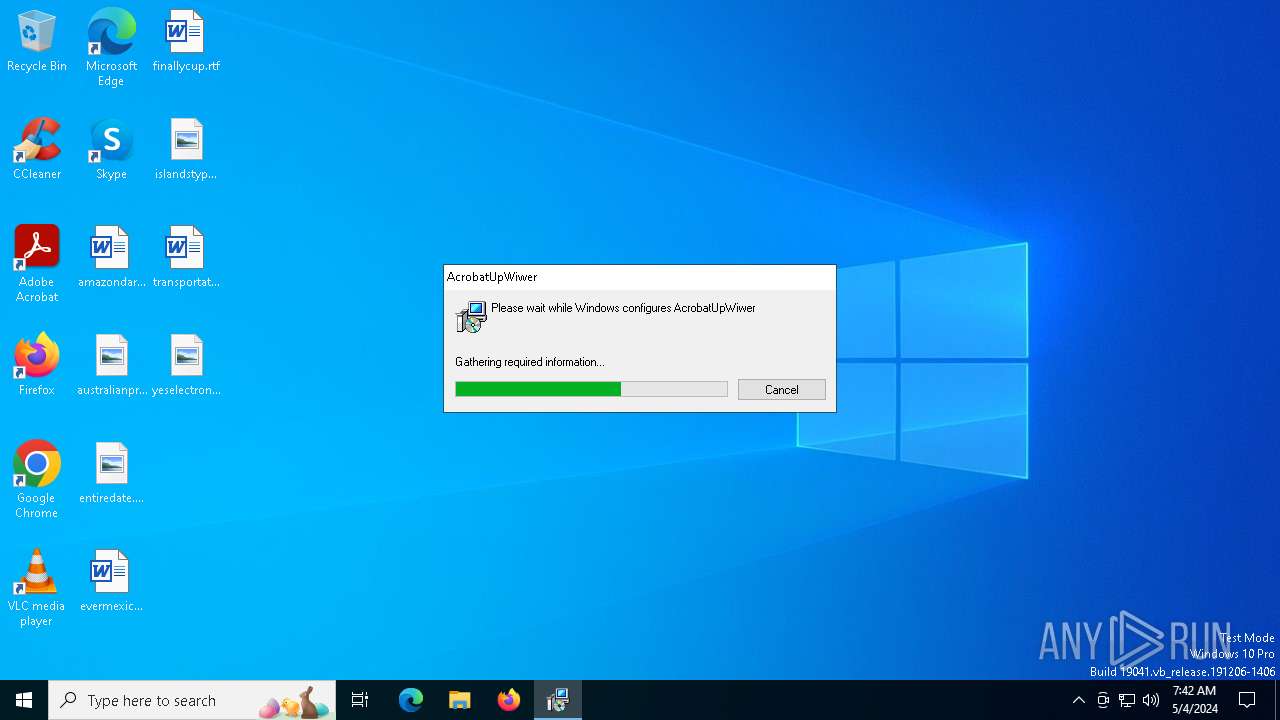
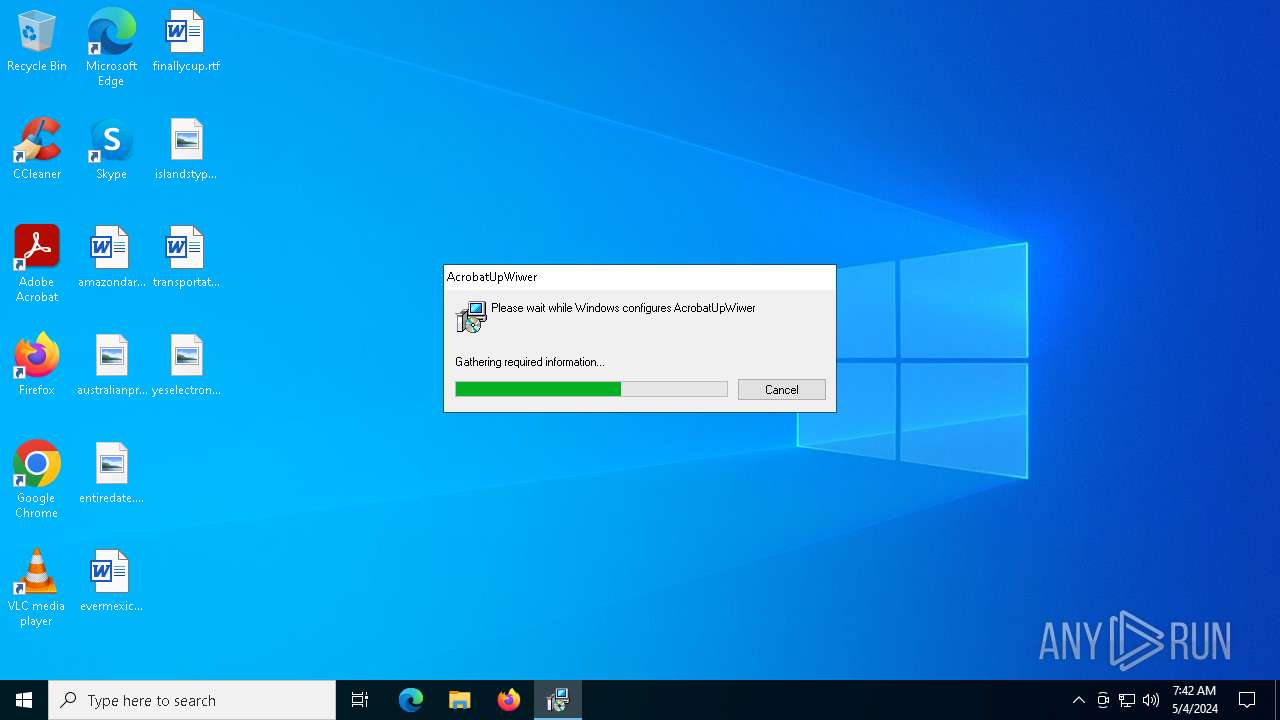
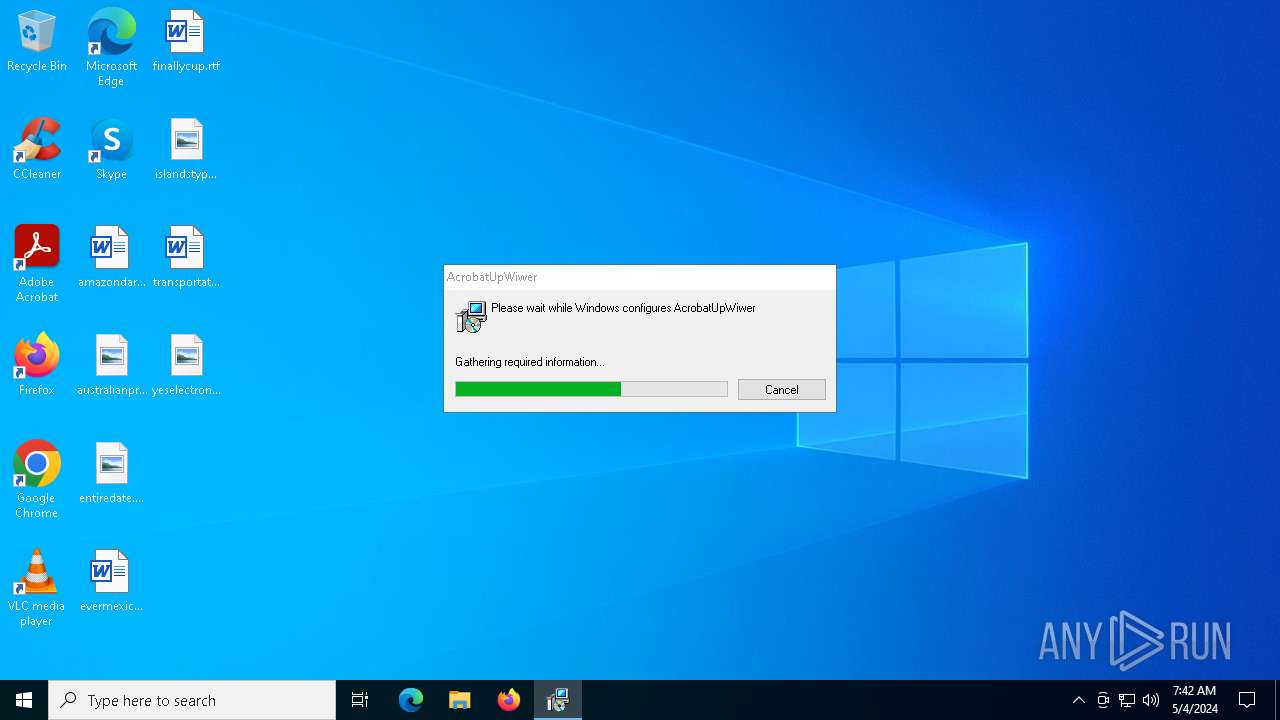
| File name: | 169c5cb4f4eac0ab52f6fbf9919918056653ef3f4d59d2727d060b62d268f272.msi |
| Full analysis: | https://app.any.run/tasks/9f5133c3-c1df-48af-8440-4ee8efce1d85 |
| Verdict: | Malicious activity |
| Analysis date: | May 04, 2024, 07:42:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {29ABADB8-3265-4048-84E0-5CB36843D182}, Number of Words: 10, Subject: AcrobatUpWiwer, Author: AcrobatUpWiwer, Name of Creating Application: AcrobatUpWiwer, Template: ;1033, Comments: This installer database contains the logic and data required to install AcrobatUpWiwer., Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Fri May 3 13:08:44 2024, Last Saved Time/Date: Fri May 3 13:08:44 2024, Last Printed: Fri May 3 13:08:44 2024, Number of Pages: 450 |
| MD5: | C982B1F284E0FEB1E83154B0D013FF79 |
| SHA1: | 426D376755EBA681D75D0325E9F0E61B28090751 |
| SHA256: | 169C5CB4F4EAC0AB52F6FBF9919918056653EF3F4D59D2727D060B62D268F272 |
| SSDEEP: | 12288:6mLo9IjHt+eorXVVVKVlv0VVVVVV9vj9VjjkKmx2c/aBut+OBp+TW0Cxef/TZCk6:6mk9IjHPo645But++pb4ZF7Lva |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 6428)
PHISHING has been detected (SURICATA)
- msiexec.exe (PID: 6428)
Changes the autorun value in the registry
- aeadminnull.exe (PID: 5576)
SUSPICIOUS
Checks Windows Trust Settings
- msiexec.exe (PID: 6360)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6360)
Reads the date of Windows installation
- msiexec.exe (PID: 6428)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6428)
- aeadminnull.exe (PID: 5576)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 6428)
The executable file from the user directory is run by the CMD process
- aeadminnull.exe (PID: 5576)
INFO
An automatically generated document
- msiexec.exe (PID: 6240)
Checks supported languages
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 6428)
- aeadminnull.exe (PID: 5576)
Reads the computer name
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 6428)
- aeadminnull.exe (PID: 5576)
Reads the software policy settings
- msiexec.exe (PID: 6240)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 6428)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6240)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6360)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 6428)
Process checks computer location settings
- msiexec.exe (PID: 6428)
Reads Environment values
- msiexec.exe (PID: 6428)
- aeadminnull.exe (PID: 5576)
Checks proxy server information
- aeadminnull.exe (PID: 5576)
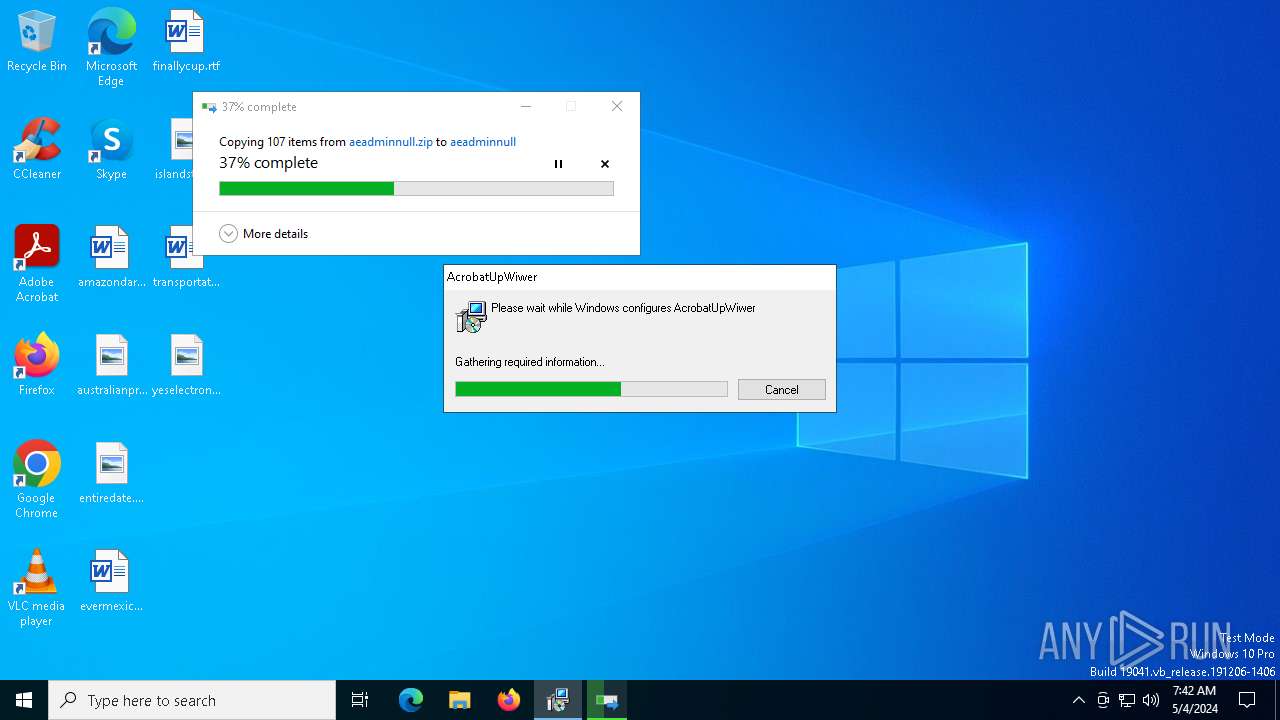
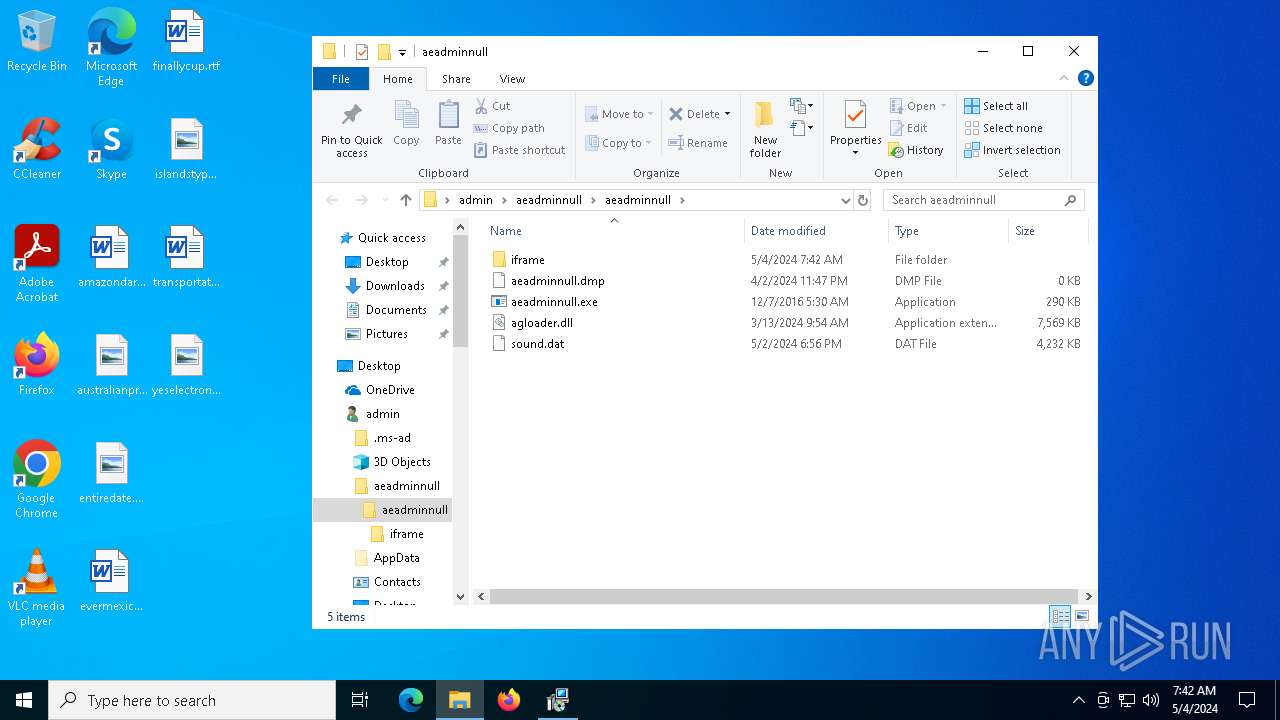
Creates files or folders in the user directory
- aeadminnull.exe (PID: 5576)
Creates a software uninstall entry
- msiexec.exe (PID: 6360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Pages: | 450 |
|---|---|
| LastPrinted: | 2024:05:03 13:08:44 |
| ModifyDate: | 2024:05:03 13:08:44 |
| CreateDate: | 2024:05:03 13:08:44 |
| Keywords: | Installer, MSI, Database |
| Title: | Installation Database |
| Comments: | This installer database contains the logic and data required to install AcrobatUpWiwer. |
| Template: | ;1033 |
| Software: | AcrobatUpWiwer |
| LastModifiedBy: | - |
| Author: | AcrobatUpWiwer |
| Subject: | AcrobatUpWiwer |
| Words: | 10 |
| RevisionNumber: | {29ABADB8-3265-4048-84E0-5CB36843D182} |
| CodePage: | Windows Latin 1 (Western European) |
| Security: | None |
Total processes
138
Monitored processes
12
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6240 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\169c5cb4f4eac0ab52f6fbf9919918056653ef3f4d59d2727d060b62d268f272.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6360 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6428 | C:\Windows\syswow64\MsiExec.exe -Embedding 20EFA0D57C33660C88E243E0A14CE7D1 | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6720 | "C:\Windows\System32\cmd.exe" /C mkdir C:\Users\admin\aeadminnull\ | C:\Windows\SysWOW64\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6732 | "C:\Windows\System32\cmd.exe" /C mkdir C:\Users\admin\aeadminnull\aeadminnull | C:\Windows\SysWOW64\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6740 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6752 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4148 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6616 | "C:\Windows\System32\cmd.exe" /c start C:\Users\admin\aeadminnull\aeadminnull\aeadminnull.exe | C:\Windows\SysWOW64\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6156 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 949
Read events
18 829
Write events
111
Delete events
9
Modification events
| (PID) Process: | (6360) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: D81800000DA0859FF69DDA01 | |||
| (PID) Process: | (6360) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 5BB1C5800367342916A43809206F86079FF9E2E1BDEBD51823E7E397BB96318E | |||
| (PID) Process: | (6360) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (6428) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings |
| Operation: | write | Name: | JITDebug |
Value: 0 | |||
| (PID) Process: | (6428) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6428) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6428) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6428) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6428) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\Component Categories\{56FFCC30-D398-11D0-B2AE-00A0C908FA49}\Enum |
| Operation: | write | Name: | Implementing |
Value: 1C00000001000000E80705000600040007002A0033007C00010000001E768127E028094199FEB9D127C57AFE | |||
| (PID) Process: | (6428) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000009C1EA4AAF69DDA01 | |||
Executable files
10
Suspicious files
80
Text files
1
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6360 | msiexec.exe | C:\WINDOWS\Installer\113805.msi | executable | |
MD5:C982B1F284E0FEB1E83154B0D013FF79 | SHA256:169C5CB4F4EAC0AB52F6FBF9919918056653EF3F4D59D2727D060B62D268F272 | |||
| 6428 | msiexec.exe | C:\Users\admin\aeadminnull\aeadminnull\agloader.dll | executable | |
MD5:E49204B99B9AB9A2E29740CE40E78707 | SHA256:5AB83A110AFBDBEEF890A5202CD042E2B338B8EC760501CB6D1A73450478DAD3 | |||
| 6428 | msiexec.exe | C:\Users\admin\null.ini | text | |
MD5:85F4067B8210A013482B1CACC3C46645 | SHA256:8E6075409586827759CDF242E43E47208E96A48B9D1C1E0B1E4A9D97424E15F3 | |||
| 6428 | msiexec.exe | C:\Users\admin\aeadminnull\aeadminnull\iframe\rolloutfile.tv1.3.tv | binary | |
MD5:C5A27652BFEF12D580F8C7D9278BFB56 | SHA256:84239C96D1A3EEA8F4A1131EE859C70863D2D2FF981DB955A204D06FB3E399F9 | |||
| 6360 | msiexec.exe | C:\WINDOWS\Installer\MSI396C.tmp | executable | |
MD5:5A1F2196056C0A06B79A77AE981C7761 | SHA256:52F41817669AF7AC55B1516894EE705245C3148F2997FA0E6617E9CC6353E41E | |||
| 6360 | msiexec.exe | C:\WINDOWS\Installer\MSI3BA1.tmp | executable | |
MD5:5A1F2196056C0A06B79A77AE981C7761 | SHA256:52F41817669AF7AC55B1516894EE705245C3148F2997FA0E6617E9CC6353E41E | |||
| 6428 | msiexec.exe | C:\Users\admin\aeadminnull\aeadminnull\aeadminnull.zip | compressed | |
MD5:A058E8449BC2774850CA90C5408E7F70 | SHA256:98C5365EB09DD3A2C31B88950811F6DC941562CF2713E41C49FCF912D026F332 | |||
| 6428 | msiexec.exe | C:\Users\admin\aeadminnull\aeadminnull\iframe\rolloutfile.tv10.1.tv | binary | |
MD5:0F47D734176C343CF3FBE700D08D0062 | SHA256:61D82DE1D9F5DF0B5F96C7F4E1CB249E3A41A49A3225FA2C58E781E0AA8AC351 | |||
| 6428 | msiexec.exe | C:\Users\admin\aeadminnull\aeadminnull\iframe\rolloutfile.tv11.1.tv | binary | |
MD5:8912777F68DD57322A21A454A3038289 | SHA256:26F01B5F8468B8E78D88232717D2785C9EAEC35F239820AFB0DDA382297A0830 | |||
| 6360 | msiexec.exe | C:\WINDOWS\Installer\MSI3AF4.tmp | executable | |
MD5:5A1F2196056C0A06B79A77AE981C7761 | SHA256:52F41817669AF7AC55B1516894EE705245C3148F2997FA0E6617E9CC6353E41E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
50
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5260 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
6420 | SIHClient.exe | GET | 200 | 2.18.97.123:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
6420 | SIHClient.exe | GET | 200 | 2.18.97.123:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
5004 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
4264 | svchost.exe | GET | 200 | 88.221.125.143:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
4680 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | — | — | unknown |
5576 | aeadminnull.exe | GET | 200 | 45.178.181.171:80 | http://hotelconsolidormalve.com.br/conta/inspecionando.php | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4364 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
4264 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1964 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5140 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4264 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6428 | msiexec.exe | 149.137.137.254:443 | faturasgerada.s3.us-east-005.backblazeb2.com | — | US | unknown |
4264 | svchost.exe | 88.221.125.143:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
5140 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
faturasgerada.s3.us-east-005.backblazeb2.com |
| unknown |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6428 | msiexec.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Phishing domain observed in TLS SNI (s3.us-east-005 .backblazeb2 .com) |
Process | Message |
|---|---|
aeadminnull.exe | C:\Users\admin\AppData\Roaming\AGData\config.json |